Next: Checkpointing for Recovery
Up: Figures in the book
Previous: Failure Detectors
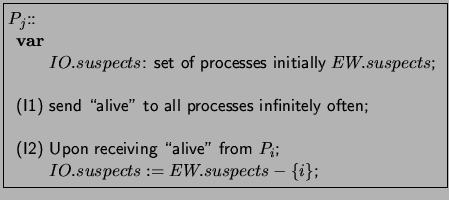
Figure:
Implementation of an IO detector using a
 detector
detector
|
|
Figure:
Implementation of an IO detector
|
|
Figure:
A detector that does not satisfy IO accuracy
|
|
Figure:
An algorithm for the alive token problem
|
|
Figure:
An algorithm that eventually guarantees a single token
|
|
Figure:
An algorithm for solving the  -set consensus problem
-set consensus problem
|
|
Figure:
An algorithm for reliable broadcast of message 
|
|



Next: Checkpointing for Recovery
Up: Figures in the book
Previous: Failure Detectors
Vijay K. Garg
2005-02-08